Infosec Newbie

[Updated 20/07/2018]
I have recently started a career in Cyber Security / Information Security. My path, somewhat recent might be useful for those just starting out. A few of these guides have cropped up but everyone has a unique path or story. I've met like minded individuals along the way and have swapped numerous tips which might be handy to someone just starting out.
Social Media Community.
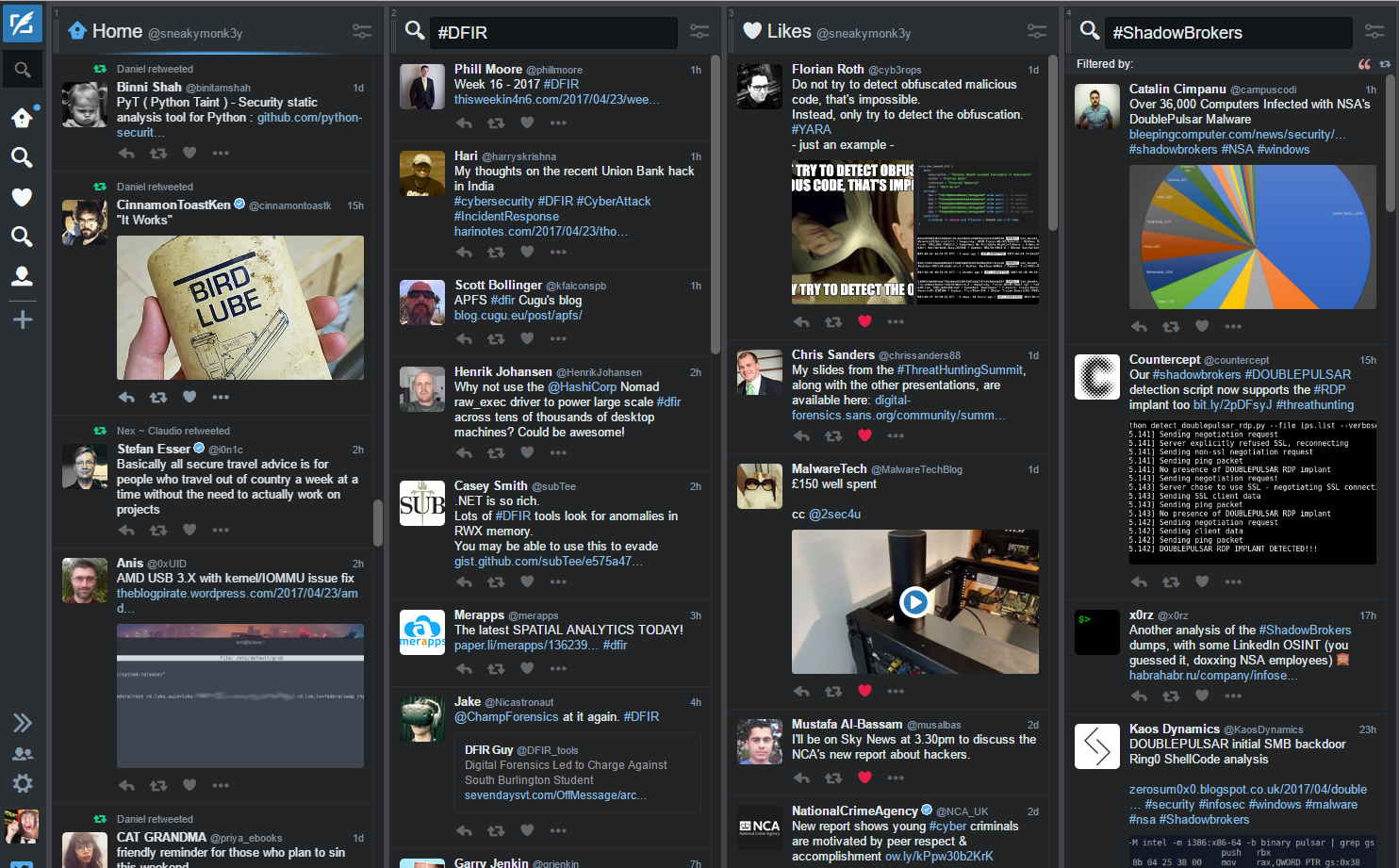
I use twitter to keep up to date with the community. Some of the most biggest names in the industry hang out on Twitter and if you need to ask a question Twitter is pretty much the medium to go for.
My Top 50 infosec peeps to follow, from here pivot away depending on your interest. List contains, social engineers, penetration testers, malware researchers, incident responders, hardware/IoT hackers, tool developers, security awareness advocates, investigative reporting journalists, certified infosec instructors, newbies (follow their paths), threat intel analysts and other 'infosec rockstars'.
- Kevin Mitnick @kevinmitnick
- Darren Kitchen @hak5darren
- James Lyne @jameslyne
- Rob Fuller @mubix
- Hacker Fantastic @hackerfantastic
- Robin @digininja
- JΞSŦΞR ✪ ΔCŦUAL³³º¹ @th3j35t3r
- Mikko Hypponen @mikko
- Chris Sanders @chrissanders88
- Bʀʏᴀɴ @Bry_Campbell
- briankrebs @briankrebs
- Kevin Breen @KevTheHermit
- Steve Armstrong @Nebulator
- Travis Smith @MrTrav
- Ken Munro @TheKenMunroShow
- Jason Trost @jason_trost
- MalwareTechLab @MalwareTechLab
- Florian Roth @cyb3rops
- Kevin Beaumont @GossiTheDog
- x0rz @x0rz
- Eric Zimmerman @EricRZimmerman
- Malware Unicorn @malwareunicorn
- Matt Bennett @ma77bennett
- Will @harmj0y
- Liam Randall @Hectaman
- Dave Kennedy (ReL1K) @HackingDave
- Jack Crook @jackcr
- John Lambert @JohnLaTwC
- Tavis Ormandy @taviso
- linkcabin @LinkCabin
- Dan (4n6k) @4n6k
- Samy Kamkar @samykamkar
- Eric Conrad @eric_conrad
- Roberto Rodriguez @Cyb3rWard0g
- Sev @sudosev
- Troy Hunt @troyhunt
- Jess @drjessicabarker
- chris doman @chrisdoman
- Brad @malware_traffic
- John Matherly @achillean
- the grugq @thegrugq
- SwiftOnSecurity @SwiftOnSecurity
- JaysonEStreet @jaysonstreet
- Andy | ゼフラフィッシュ @ZephrFish
- Mark Russinovich @markrussinovich
- Kris McConkey @smoothimpact
- Robert M. Lee @RobertMLee
- Sean 🔱 @zseano
- DEY! @DEYCrypt
- Seth Hall @remor
- Gary Hoffman @PortUnreachable
- Colin Hardy @cybercdh
- Nick Carr @ItsReallyNick
- Christopher Glyer @cglyer
- Casey Smith @subTee
- Daniel Bohannon @danielhbohannon
- Matthew Dunwoody @matthewdunwoody
- ippsec @ippsec
- Tyler Hudak @SecShoggoth
- [ REDACTED ] @porthunter
- Alex Davies @pwndizzle
Another trending platform is Medium, you can sign up with your Twitter account.
This offers a simple blogging platform. Again, follow the same people off Twitter to get a foothold of who posts frequently. Most topics that are discussed on Twitter normally get thrown over to Medium for a technical deep dive, it really depends on who you follow.
Nearly missed adding this gem. https://www.reddit.com/r/netsec/ is an excellence source of community opinions and resources.
Security Conferences.
These keep you on the cutting edge.
They can seem daunting at first but just bite the bullet and go. Everyone is like minded and here for the same reason - a passion for all things security. Maybe start off with the more local conferences and build a network up before attending any of the international or more expensive conferences.

You don’t have to attend even these expensive Blackhat/Defcon/44con conferences. Most post their videos within hours/days onto Youtube. I’d recommend for you to attend Security B-Sides London/Manchester, Steelcon (Sheffield), 44con (London), Passwords (Cambridge), OWASP (local), DEFCON (local) which are all very community driven and most are free or just a small fee. I'm sure there are ones I've missed. Sorry :)
- https://www.youtube.com/user/irongeek <- this is awesome!
- https://www.youtube.com/user/HackersOnBoard
- https://www.youtube.com/user/robtlee73
- https://www.youtube.com/user/BlackHatOfficialYT
- https://www.youtube.com/user/teamcymru
- https://www.youtube.com/user/DEFCONConference
- https://www.youtube.com/channel/UCpNGmljppAJbTIA5Msms1Pw/videos
- https://www.youtube.com/channel/UCXXNOelGiY_N96a2nfhcaDA
- https://www.youtube.com/channel/UCP28F4uf9s2V1_SQwnJST_A
- https://www.youtube.com/channel/UCv6i6WVf-KeUeXFmp9oy29w
Blog.
I’d heavily recommend a blog, set yourself a cheap VPS on Vultr / Digital Ocean - great one click blog options available (referal link here with $10 credit) - or just get a free
Medium/
Blogger / LinkedIn account and go from there.
Use this to attempt a few CTF challenges and write them up? Don’t worry about starting with basics. Check out https://www.vulnhub.com/ for examples from other peoples posted ‘walk throughs’ or just post a project you are working on in your home lab environment.
Finally, this can act as your online CV which resonates REALLY well with employees as it’ll give you an edge straight away.
Books.
Still a go to even if they grow old fast.
Digital books. Sign up to No Starch Press as sometimes they have PDF/eBook specials which I’ve used to load up on my Kindle plenty of times before. Humble Book deals are awesome, subscribe and keep an eye out for when they become live to grab a bargain set of eBooks too.
Literally my book shelf (some missing or at work, see list below)
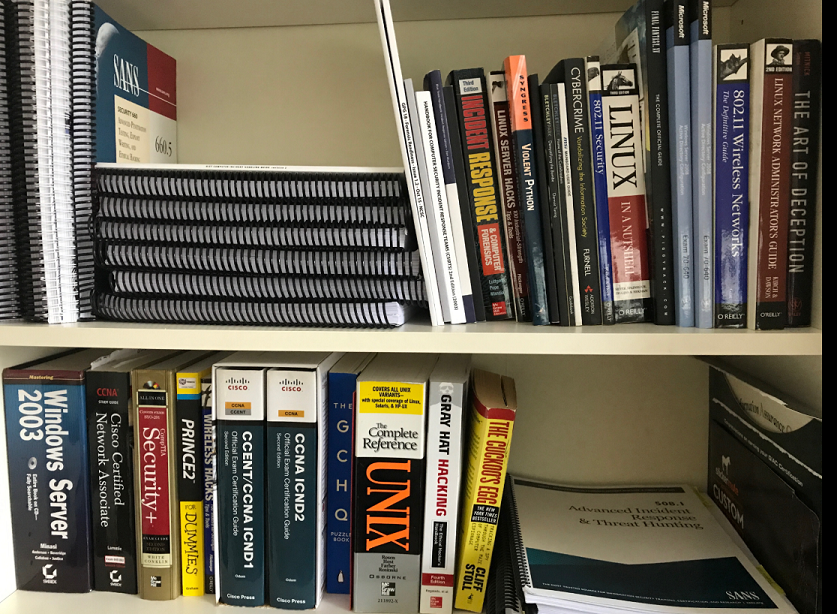
These are the best which I heavily recommended (in no order)
- RTFM: Red Team Field Manual
- Blue Team Handbook: Incident Response Edition: A condensed field guide for the Cyber Security Incident Responder
- The Hacker Playbook 2: Practical Guide To Penetration Testing
- Black-Hat-Python-Programming-Pentesters
- Hacking-Ethical-Hackers-Handbook-Fourth
- Violent-Python-Cookbook-Penetration-Engineers
- Web-Application-Hackers-Handbook-Exploiting
- Nmap-Network-Scanning-Official-Discovery
- Art-Memory-Forensics-Detecting-Malware
- Malware-Analysts-Cookbook-DVD-Techniques
- Practical-Malware-Analysis-Hands-Dissecting-Malicious-Software
- Applied Network Security Monitoring: Collection, Detection, and Analysis
- Network Security Assessment 3rd Edition
Another useful tip is the digital book collection over at Safari Books Online. If you tweet the account '@safarlbookshelp / @safari' and ask nicely, they might give you a discount for the monthly subscription that is normally ~£30 per month (Thanks @CyberJocko). Although quite expensive, you have some of the best books being constantly updated and can be synchronised across many devices.
Last but not least - The SANS Reading Room is a hidden gem boasting over 2,660 original computer security white papers in 102 different categories and has 75k visitors a month and is completely FREE! A personal favourite. You can submit a Gold Paper once you are GIAC certified (passed any SANS exam) but this is subject to an application and fee around a few hundred dollars (link).
Some other nuggets of information can be found over at NIST and the NCSC - National Cyber Security Centre (UK) Guidance section here.
Podcasts.
Useful source of infosec discussions and daily news when scrolling through RSS feeds and Twitter isn't your cup of tea.
For iPhone I just use the built in player but for Android I paid for the "Podcast & Radio Addict" app. I found myself subscribing to way to many and never got round to listening to them all, these are the ones I frequently go to.
Competitions.
UK focused
Just head over to Cyber Security Challenge UK. They host entry level to 'Masterclass' types of CTF competitions covering a range of infosec areas. Win prizes, build your network and hopefully land a new job! I went to many face to face challenges and secured two Masterclass finals which pretty much jump started my infosec career. Highly recommend!
SANS Cyber Academy / SANS Retraining Academy - A more recent 'boot camp' style offered by SANS Institute that are the leaders in security training. Keep an eye out for their applications to their programmes via Twitter / official site to see what they do each year. I was lucky enough to get sponsored for the Cyber Academy in 2015.
CTFs.
[Capture The Flag/s] (Cyber Security Gamification) A system/s purposely set up to practice or learn new skills by acquiring hidden flags located in one of many places. Normally they're codes which when submitted will grant you points or access to further levels.
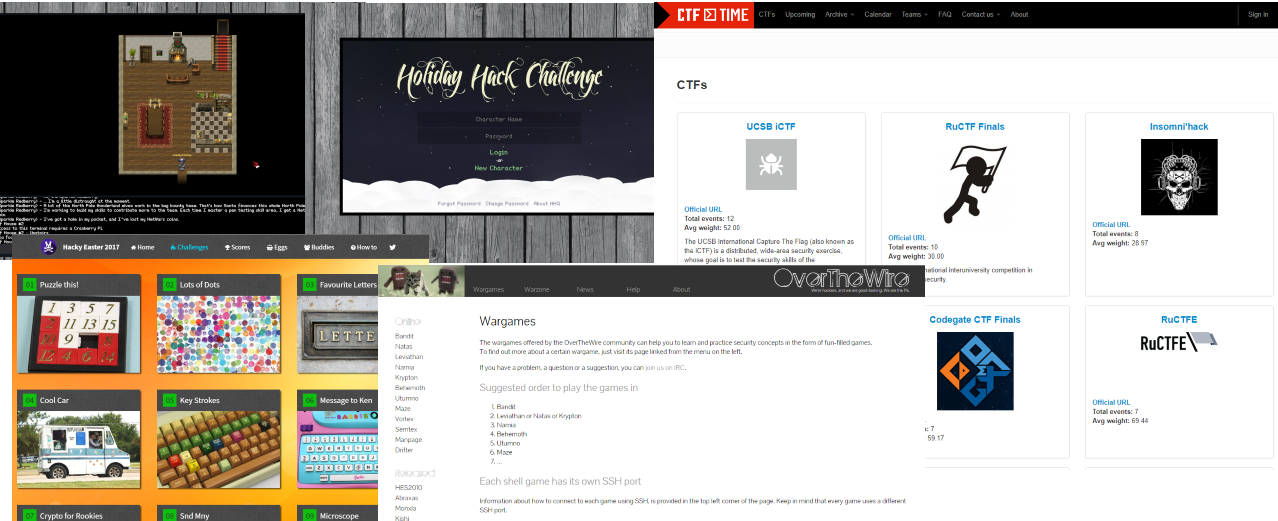
Try the below;
-
Cyber Security Challenge runs a PoD CTF system, head over to https://cybersecuritychallenge.org.uk/competitions/play-demand-cyphinx
-
"PentesterLab provides vulnerable systems that can be used to test and understand vulnerabilities". Web for Pentester I & II are best to start with.
Also one to note. These OSCP style 'boot2root' VMs have been favourable from the community;
- SickOs 1
- SickOS 1.2
- Kioptix Level 1
- Kioptix Level 2
- Kioptrix2014
- KioptrixVM3
- pWnOS v2.0
- Stapler
- Tr0ll
- Tr0ll2
- Vulnix
- VulnOSv2
- FristiLeaks 1.3
- LordOfTheRoot 1.0.1
- mrRobot
- pwnlab_init
-
Hack The Box Hack The Box is an online platform allowing you to test your penetration testing skills and exchange ideas and methodologies with other members of similar interests. Recently come across this and managed to only register at this moment in time. Seems popular with OSCP students.
-
OverTheWire hosts a number of war games ranging from basic Linux use (bandit) through cryptography (Krypton) to binary exploitation (Narnia).
-
picoCTF is a great way to hone your skills in many of the areas listed above and provides a fantastic introduction to these types of challenges.
-
Seasonal challenges. Both are excellent, SANS Holiday Hack Challenge and Hacking Labs Hacky Easter
-
CTF-Time is pretty much where 'professional' CTF teams keep track of their scores but it is also the defacto event listing of most if not all CTFs out there to play.
If you get stuck, you'll have to wait for the write ups but older CTFs might give you hints.
Check out ippsec's @ippsec YouTube channel for HTB videos.
Industry Certificates.
These are not essential to learning but are helpful to get that foot in the door.

OSCP (syllabus here) is very popular within the industry and is known as stated on their website 'world’s first completely hands-on offensive information security certification'. OSCP is roughly $800 / ~£600 and is self-paced training programme with a final 24 hour exam inside a lab/sandpit environment. You must root enough boxes to pass and then provide a report on how you popped each one. See note taking section further down the page. Some more pricing options are below;
- The cost for this course with 30 days of labs is: 800$ USD
- The cost for this course with 60 days of labs is: 1000$ USD
- The cost for this course with 90 days of labs is: 1150$ USD
Some further exam details here;
https://support.offensive-security.com/#!oscp-exam-guide.md
https://support.offensive-security.com/#!pwk-reporting.md
https://www.offensive-security.com/pwk-online/PWK-Example-Report-v1.pdf
Another Offensive Security project is https://kali.training/. They have also just released Kali Revealed 1st Edition - Mastering the Penetration Testing Distribution.
CREST - Quite UK driven but has grown tremendously over the last few years and has gained a lot of industry recognition. These exams are a mix of multiple choice and hands on lab exams. Price range starts at £200 - £1600 so be wary of cost here. One of the best aspects is that CREST provide a detail syllabus for each exam as well as training materials such as recommended books! A popular exam is the CREST CRT - Registered Tester (aka Penetration Tester), which is now obtainable if you pass your OSCP (+ a small fee to CREST) explained here OSCP and CRT Equivalency.
SANS - (Curricula) - are another great training provider but are way expensive to start off. The course instructors are world class when it comes to their field so you know you are being trained by the best hence the price tag. You can possibly self study if you know the right materials for the exam you wish to sit (not normally published) and then you can go attempt an exam (~£1000+). If you choose this method you will need to apply as this is not the normal certification route. SANS is definitely one to consider once you have probably moved into the info sec area but be aware of their Cyber Academy and Cyber Retraining programmes they run annually.
Others. CEH is well known and so is CiSSP. CEH has lost a bit of credibility over the past few years but can be still useful for entry level requirements. CiSSP is a broad certification covering many topics and is normally seen on the trailing end of management and business leader's email signatures. You will need 5yrs+ of related security experience and a reference from another certified member before you are eligable for sitting the 6hr 250+ question exam.
Previous Experience in IT.
Not necessarily security but it helps to have a background in Systems Administration, Networking or Programming. Either will give you the fundamentals that back any security related job. Failing this experience, an IT fundamentals course (CompTIA Network+ Security+ etc..) or University computer degree will help you out here. There are numerous videos on Youtube and places such as PluralSight and Cybrary that can help on the cheap. Understand the basics and then move forward.
Lab Environments.
Best advice.
You must set a lab up or have a PC where you can play around with tools/OS'es. This hands on learning is key to constantly improving your skill set. As discussed above, virtualised environments are heavily used for the lab exams for OSCP and CREST CRT - take note, there is nothing stopping you creating your own lab of vulnerable machines. Check out metasploit-unleashed to quickly set up Kali and Metasploitable v2.
Another great resource is Project Avatar by @da_667. This 586 paged 'Architecting Virtual Machine Labs' guide is very comprehensive and is a great reference tool.
You will see a lot of demos at conferences where speakers will spin up vms to showcase their latest stuff. Do the same with VMware or Virtualbox on your kit at home. Use Microsoft's OneNote (great for screen clipping / diagramming!) / Google Keep / Evernote / CherryTree to document what you're doing and then even convert this into a blog post? Either way, take plenty of notes while you learn for reference later. This is an underestimated skill. Imagine trying to explain how you exploited a vulnerability or how you forensically found out an intrusion in your environment hours after you have resolved or finished your job. Document as you go.
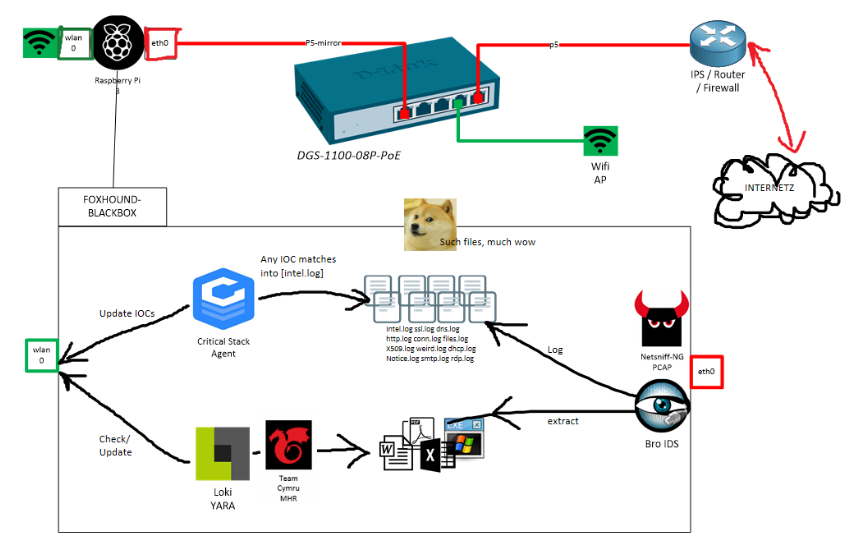
Example of my home IDS project https://sneakymonkey.net/2016/10/30/raspberrypi-nsm/
Conclusion
Just get stuck in. GO.


